Natural disasters are an unavoidable part of life. But their impact on businesses can be reduced if they’re prepared and fully compliant with acceptable disaster recovery protocols.
Understanding NFPA Electrical Codes and Disaster Recovery Protocols


Natural disasters are an unavoidable part of life. But their impact on businesses can be reduced if they’re prepared and fully compliant with acceptable disaster recovery protocols.
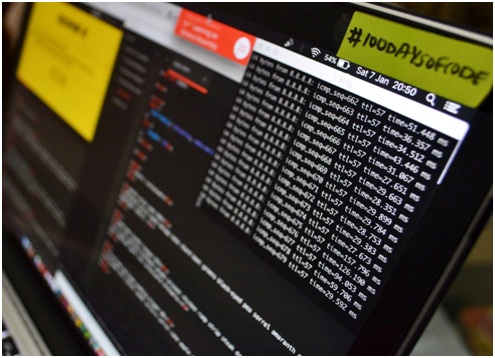
2019, so far, has been ayear of significant state-level breaches, forcing enterprises to look closer into their data security approaches. Headlines constantly feature cyber attacks of major corporations like Facebook, Marriott and Toyota — leaving millions at risk. Experts believe that cybercrime is one of the biggest challenges that we’ll have to face in the next two decades.
Here is a checklist of characteristics that you should look for in an IT consultant when you are hiring one.

Telecommunication technology has come a long way in the past few decades. Use cases that required tons of specialized equipment 20 years ago can now be run on a simple network connection across one Gigabit Ethernet cable.

Ensuring reliable phone access is one of the first tasks that need to be taken care of when starting a business. Even though majority of the work is done on networked computers, companies still need phone services for day-to-day communication.